
Which biometric authentication methods suit enterprise apps best?
Enterprise security that creates anxiety and resistance undermines its own purpose. Authentication in business applications should feel protective, not punitive. Yet most organisations treat biometric verification as a technical checkbox rather than a human experience.
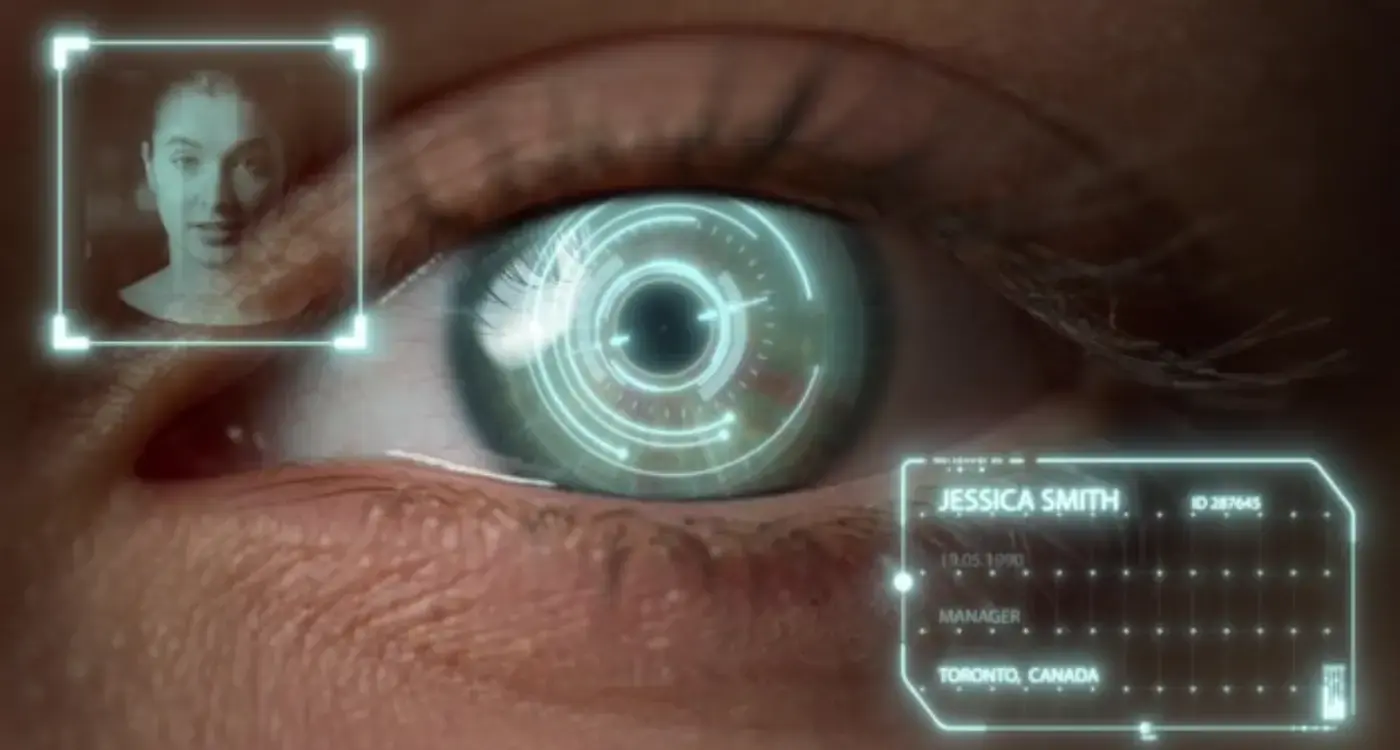
The choice between fingerprint scanners, facial recognition, voice authentication, and iris scanning involves more than comparing accuracy rates. Each method creates different emotional responses that ripple through employee productivity, stress levels, and overall willingness to engage with company systems.
Biometric authentication succeeds or fails based on how safe users feel during verification.
Understanding these psychological dynamics becomes critical when rolling out enterprise authentication. The method that performs best in laboratory conditions might create anxiety in real workplace scenarios. The technology that seems most secure on paper could generate resistance that undermines the very security it aims to protect.
Understanding Biometric Authentication in Enterprise Context
Enterprise biometric authentication operates under different pressures than consumer applications. Employees face repeated verification throughout their workday, often while managing competing priorities and deadlines. The authentication experience becomes part of their daily workflow rhythm rather than an occasional security checkpoint.
Different biometric methods create varying levels of intrusion into personal space and privacy. Fingerprint scanning requires physical contact with shared surfaces. Facial recognition operates at a distance but captures identifying features. Voice authentication needs audio input that others might overhear. Each approach carries distinct psychological implications for workplace comfort.
Consider the physical environment where authentication occurs. Open office spaces create different privacy expectations than private workstations.
The enterprise context also amplifies failure consequences. When consumer biometric authentication fails, users might feel momentary frustration. When enterprise authentication fails, employees face potential productivity loss, missed meetings, or delayed access to critical systems. This heightened stakes environment affects how people approach and experience the verification process.
The Emotional Psychology of Security Verification
Security verification triggers fundamental psychological responses around trust, control, and vulnerability. Users entering authentication flows carry emotional states shaped by their current stress levels, time pressures, and past experiences with similar systems. These emotional states directly influence how successfully biometric systems perform.
The three most common fear factors users experience during security interactions involve feeling that actions are committed and irreversible, feeling uninformed about what the system is doing, and experiencing social anxiety about potential failure in workplace settings. Enterprise biometric systems must address these fears through clear communication and predictable behaviour.
Different biometric methods evoke different emotional responses. Fingerprint scanning can feel clinical and invasive, particularly when shared devices are involved. Facial recognition might trigger privacy concerns about facial data storage. Voice authentication could create social anxiety in open workspaces where others overhear failed attempts.
Design that understands your users
We build app experiences around real user behaviour, not assumptions. Research, psychology-driven design and technical specs that turn users into loyal advocates.
How User Stress Impacts Authentication Success
Stress fundamentally changes how people interact with biometric systems. In high-stress environments, user problems stem from lower comprehension rather than inability to find interface elements. Users lose understanding of the overall process because they operate on a more emotional level, abandoning logical thinking patterns.
When comprehension drops significantly, this typically indicates high-stress environments rather than poor design.
Physical manifestations of stress also affect biometric accuracy. Sweaty fingerprints reduce scanner effectiveness. Elevated heart rates alter voice patterns. Facial tension changes the geometric relationships that facial recognition systems rely on. These physiological changes create a negative feedback loop where stress reduces authentication success, which increases stress further.
Design authentication flows that account for multiple attempts without making users feel they've failed.
The enterprise environment adds layers of social stress. Employees might worry about colleagues witnessing authentication failures or delays. They might feel pressure to complete verification quickly to avoid holding up meetings or workflows. This social dimension of workplace authentication requires careful consideration in system design and implementation.
Behavioural Patterns During Security Interactions
Users approach biometric authentication with learned behaviours from previous security experiences. These behavioural patterns provide insights into emotional states and preferences that affect authentication success. Systems can detect emotional states through multiple signals including how fast people move through the product, dwell time on particular screens, and speed of button interactions when presented with choices.
Engagement metrics reveal additional behavioural insights. Time spent in authentication flows, frequency of return attempts, and particular times of day when authentication occurs all indicate user comfort levels with different biometric methods. These patterns help identify which approaches create smoother experiences and which generate friction.
Adaptation Strategies
Behavioural data enables real-time adaptation of authentication experiences. When systems detect hesitation or repeated attempts, they can provide additional guidance or offer alternative verification methods. This adaptive approach acknowledges that optimal biometric methods vary between individuals and situations.
Monitor authentication completion rates across different times of day to identify stress patterns in your organisation.
Designing Emotionally-Aware Authentication Flows
Effective enterprise biometric authentication begins before users encounter the verification interface. Understanding what leads up to someone using authentication and their emotional state when entering the process proves absolutely critical for effective user experience design. The authentication journey starts before users actually begin verification.
Asking for permission creates better user responses even though the technical outcome remains identical. This simple change of asking for permission means people become psychologically more invested in the process because they feel they have control. The framing represents purely a tone of voice change, not a technical modification, yet produces significantly better user responses.
The best way to reduce anxiety during authentication involves education through proper framing. Making sure users understand what they're looking at, what they're about to experience, and where they are within the process can have transformative effects on emotional connection to the authentication system.
Progressive Disclosure
Information layering should respond to user emotional states rather than purely logical organisation. In high stress or anxiety situations, simplify and reduce heightened emotional levels through education and guided simplification. Design the layering based on emotional response rather than just what makes sense from a product perspective.
Measuring Authentication Experience Effectiveness
Traditional authentication metrics focus on accuracy rates and speed. Enterprise authentication effectiveness requires broader measurement that includes user satisfaction, stress indicators, and behavioural engagement patterns. Genuine emotional connection can be measured through engagement metrics because people get engaged with emotional products rather than purely functional ones.
Key indicators include session time within authentication flows, frequency of successful first attempts, social commentary about authentication experiences, and voluntary adoption rates when multiple methods are available. These behaviours stem from emotional connection rather than mere functional satisfaction.
In the first thirty seconds of authentication, users consciously and subconsciously assess multiple factors including the quality and trustworthiness of the system, whether it feels hastily implemented, clarity about what the process involves, what will be asked of them, and where they are within the overall verification journey.
- Monitor completion rates across different biometric methods
- Track user preference patterns when multiple options are available
- Measure correlation between authentication stress and subsequent productivity
- Analyse support ticket patterns related to authentication difficulties
Survey employees about authentication preferences rather than relying solely on technical performance metrics.
Conclusion
Enterprise biometric authentication succeeds when it balances security requirements with human psychological needs. The most accurate biometric technology means little if employees find ways to circumvent it due to stress, inconvenience, or privacy concerns. Effective authentication feels protective rather than intrusive.
Different biometric methods suit different enterprise environments based on physical workspace design, employee stress patterns, privacy expectations, and operational workflow requirements. Fingerprint scanning works well for individual workstations but creates hygiene concerns for shared devices. Facial recognition offers convenience but raises privacy questions. Voice authentication provides hands-free operation but struggles in noisy environments.
The choice involves understanding your specific organisational context, employee emotional responses, and operational constraints. Success comes from designing authentication experiences that account for human psychology rather than treating biometric verification as purely a technical implementation.
Most importantly, effective enterprise authentication adapts to user needs rather than forcing users to adapt to rigid technical requirements. This human-centred approach creates security systems that employees actively support rather than passively endure.
If you're evaluating biometric authentication options for your enterprise application, we'd love to discuss how emotional design principles can improve both security and user experience. Let's talk about your authentication challenges and explore solutions that work for both your security requirements and your people.
Frequently Asked Questions
Enterprise biometric authentication operates under different pressures as employees face repeated verification throughout their workday whilst managing competing priorities and deadlines. The consequences of failure are also amplified - rather than momentary frustration, enterprise authentication failures can lead to productivity loss, missed meetings, or delayed access to critical systems.
The physical environment significantly affects biometric choice, with open office spaces creating different privacy expectations than private workstations. Voice authentication might create social anxiety in open workspaces where others can overhear failed attempts, whilst facial recognition operates at a distance and may be more suitable for shared environments.
Stress fundamentally changes how people interact with biometric systems, as users enter authentication flows carrying emotional states shaped by current stress levels, time pressures, and past experiences. These emotional states directly influence how successfully biometric systems perform, making stress management a critical factor in implementation.
The three most common fear factors involve feeling that actions are committed and irreversible, feeling uninformed about what the system is doing, and experiencing social anxiety about potential failure in workplace settings. Different methods also evoke specific responses - fingerprint scanning can feel clinical and invasive, whilst facial recognition might trigger privacy concerns about data storage.
The method that performs best in laboratory conditions might create anxiety in real workplace scenarios, undermining its practical effectiveness. Biometric authentication succeeds or fails based on how safe users feel during verification, not just technical performance metrics.
No, most organisations incorrectly treat biometric verification as a technical checkbox rather than a human experience. The choice between different methods involves understanding emotional responses that affect employee productivity, stress levels, and overall willingness to engage with company systems.
Different biometric methods create varying levels of intrusion into personal space and privacy. Fingerprint scanning requires physical contact with shared surfaces, facial recognition captures identifying features at a distance, and voice authentication needs audio input that others might overhear in the workplace.
Enterprise biometric systems must address common fears through clear communication and predictable behaviour. Organisations should focus on making users feel informed about what the system is doing and ensuring the authentication process feels protective rather than punitive or invasive.
Related Articles

How Does Eye Movement Shape Better App Layouts?
Users abandon an app within the first 30 seconds if they can't find what they're looking for—that's...

Can You Really Trust a Remote Team to Build Your App?
You've got this brilliant mobile app idea that could change everything. The concept is solid, the...
